Chapter 5. Initial Configuration
The goal of this section is to teach the reader how to perform Initial Configuration on their newly installed EnGarde Secure Linux machine. By the end of this chapter you will have completed Initial Configuration and may begin using EnGarde Secure Linux.
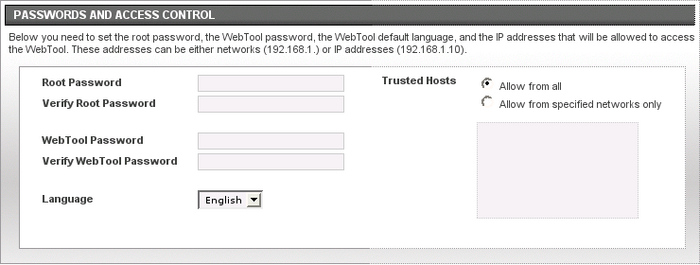
5.1. Passwords and Access Control
This section allows you to change the system passwords and define what IP addresses or networks may access the WebTool on this machine.
5.1.1. A Note About Passwords
In the following sections, and in general, it is very important to choose good passwords. Below are a few guidelines on developing good passwords:
Make sure your password is longer than six characters and contains a mix of letters, numbers, and special characters.
Never base your password off a dictionary word.
Never write your password down or share your password with anybody. Keep it safe in your head.
Never type your password while somebody is watching.
One good password method is to take a word and break it up with letters and numbers. For example, to strengthen the password lockbox, change the o's to zero's and throw in some special characters. One result would be l0ck&%b0x.
For more information on developing good passwords please refer to the following article by Ben Thomas on LinuxSecurity.com:
5.1.2. Root Password
root is the administrator account on EnGarde Secure Linux and is the only system user with full-blown privileges to access everything and anything. This field allows you to change the password for this account.
Once you have developed a password you need to enter it a second time for verification.
5.1.3. WebTool Password
This field allows you to change the password used for accessing the Guardian Digital WebTool. This password should be different from the root password but just as strong.
Once you have developed a password you need to enter it a second time for verification.
5.1.4. Language
This field allows you to select the default language that the WebTool will be presented in.
5.1.5. Trusted Host List
This field allows you to define which hosts and/or networks are permitted to access the Guardian Digital WebTool on this machine. You should keep this list as small as possible -- the more people you open up access to, the greater the threat.
You may enter individual IP addresses (ie, 192.168.1.90) or entire networks (ie, 192.168.1.0).